Ages ago, i built a php app for processing pdfs made of mupdf. i even made a go at a MacOS version. it was never very good and it broke with MacOS updates. This new complete rewrite now available! enjoy.
Product page can be found here.
Software
Ages ago, i built a php app for processing pdfs made of mupdf. i even made a go at a MacOS version. it was never very good and it broke with MacOS updates. This new complete rewrite now available! enjoy.
Product page can be found here.
I had a great time this year. i went deep into the sticker game and spent WAY too much time playing with the badge. Playing with the badge allowed me to meet and work with some incredible people with whom we learned, laughed, and lamented the badge’s terrible supplied SD cards. This year i brought flyers to promote my phone adventure game and joined in #StickerLife with a supply of stickers of my own. unfortunately the printers gave me too many flyers, but not enough stickers.
My game did get some traction this year for the first time. Still no winners, but i did get this incredible voicemail from one of the players. I appreciated more ridiculous phone stuff. great job whoever you are! EDIT: i think i found you Foxbox!
The Badge had a lot of problems. only some of which were patched with updates. I excitedly made changes, but then the SD card would fail and be unable change back. currently mine is stuck as a Mario Game, which is not so terrible. i can finish the Defcon GameBoy game on an emulator.






This project was cannibalized over a year ago. With Raspberry Pi as difficult to get ahold of as they’ve been, i thought this project might never come back to life. I launched a number of pi liberating ideas with some success. I now have enough for both fun personal projects and to get my work done. I felt i should explain the name wardriving. It is a variation on wardialing. Wardialing was trying phone numbers, looking for interesting things on the phone. Wardriving is similarly driving around looking for interesting things in the air.
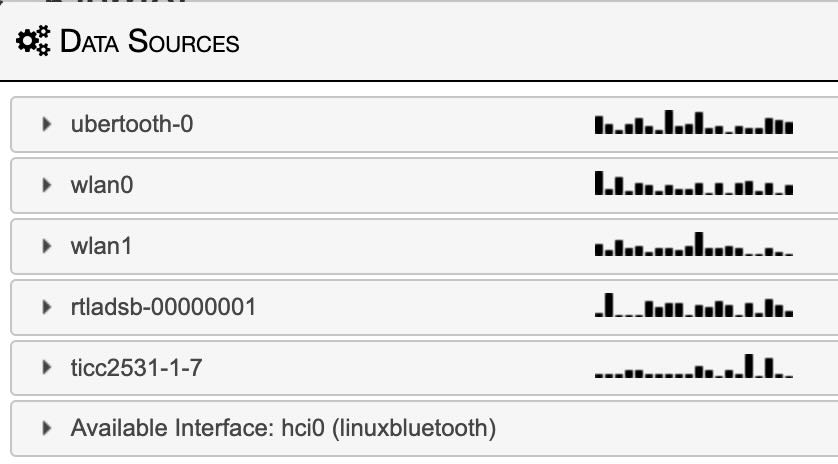
My wardriver is not pictured above, but these Pi are ready for whatever comes next. I’ve recovered an assortment of different Pi from original B+ (pi-hole) to a 2GB Pi 4 (broken helium miner). One of the best parts of this setup is the early Pi 3 (not B+). This was a lucky find as it consumes less energy and produces much less heat. With only 6 radios running (including GPS) the lower performance hasn’t been an issue, but the reduced power has been incredible. Early testing has me getting an additional 20-40% battery life vs the original pi 4 configuration. my cable management has also improved with this iteration. The setup fits in a small box in my trunk instead of a tangled mass of wires in a large bin (prototyping is fun). The reason power is so important because, believe it or not, the amperage you can pull out of a Tesla for accessories is limited. Without an alternator dumping piles of unclean energy i am forced to resort to BYOB (bring your own battery). I got a monster battery to power the Pi 4 and even more radios and accessories of the original prototype.
It is fun using the ADSB live tracker in Los Angeles as there are always planes above. Next step will be DJI drone tracking and some sort of dashboard indicator/control. I started a WiGLE account, it’s off to a pretty good start. i found a few APs, but i’m still figuring out how to share BT. maybe i’ll join the #HardHatBrigade group.




Thanks to the exceptional work by justcallmekoko, RogueMaster, and many others there is now native flipper support for the unofficial Marauder firmware for the Flipper dev-board. Marauder is firmware for the ESP-32 chipset full of security tools for bluetooth and wifi. The Flipper dev board doesn’t support bluetooth, but the wifi tools work and are usable from the flipper itself. I cannot wait to see what comes next.
After years of anticipation and excitement, my Flipper Zero has arrived! Software is still early yet, so I haven’t done much more than clone and store RFID, NFC, and IR signals. i am excited to see the interesting things me and my new dolphin friend will get up too.


I’ve been automating SSL renewals for almost as long as i’ve been deploying them. for the most part, it is very smooth and easy to do. (thanks mostly to certbot and the hard work over at let’s encrypt) The trouble comes up with non publicly addressable servers and other custom setups. cough cough. . . Unifi. . . cough cough.
I recently discovered a tool that makes all those complicated setups as easy as the original certbot installs. acme.sh is that tool. two lines! not since screen have i regret any time i spent not using such a tool.
./acme.sh –renew -d “unifi.domain.com”
./acme.sh –deploy -d “unifi.domain.com” –deploy-hook unifi
I’m doing experiments with UTM to create a single purpose XP system with zero network access. in this picture, i am trying to fix a damaged system while simultaneously installing a fresh one. eventually got it working like a champ, and now it’s almost as portable as an app. Huge thanks to 4PCTechs for your insights and archive of ancient drivers!
I’ve played with Big Sur, but i’ve had serious reservations about running it on one of my primary machines. Apple backpedaled a bit on some of their decisions and i decided i didn’t have enough problems in my life. So tonight i’m jumping in with both feet to see how it goes and what breaks. This may turn out to be a huge mistake. We’ll soon see.
Not off to a great start so far. Upgrades beget upgrades. After a few rounds of up updating my 3rd party software my system is humming even better than before. Finder is still clunky and has a tendency to hang in the most annoying ways, but they’ve added a few new tricks and an updated look. Am i the only one who misses the brushed metal phase of UI?